AI for the Enterprise SOC
Every Endpoint Alert Investigated. Not Just Triaged.
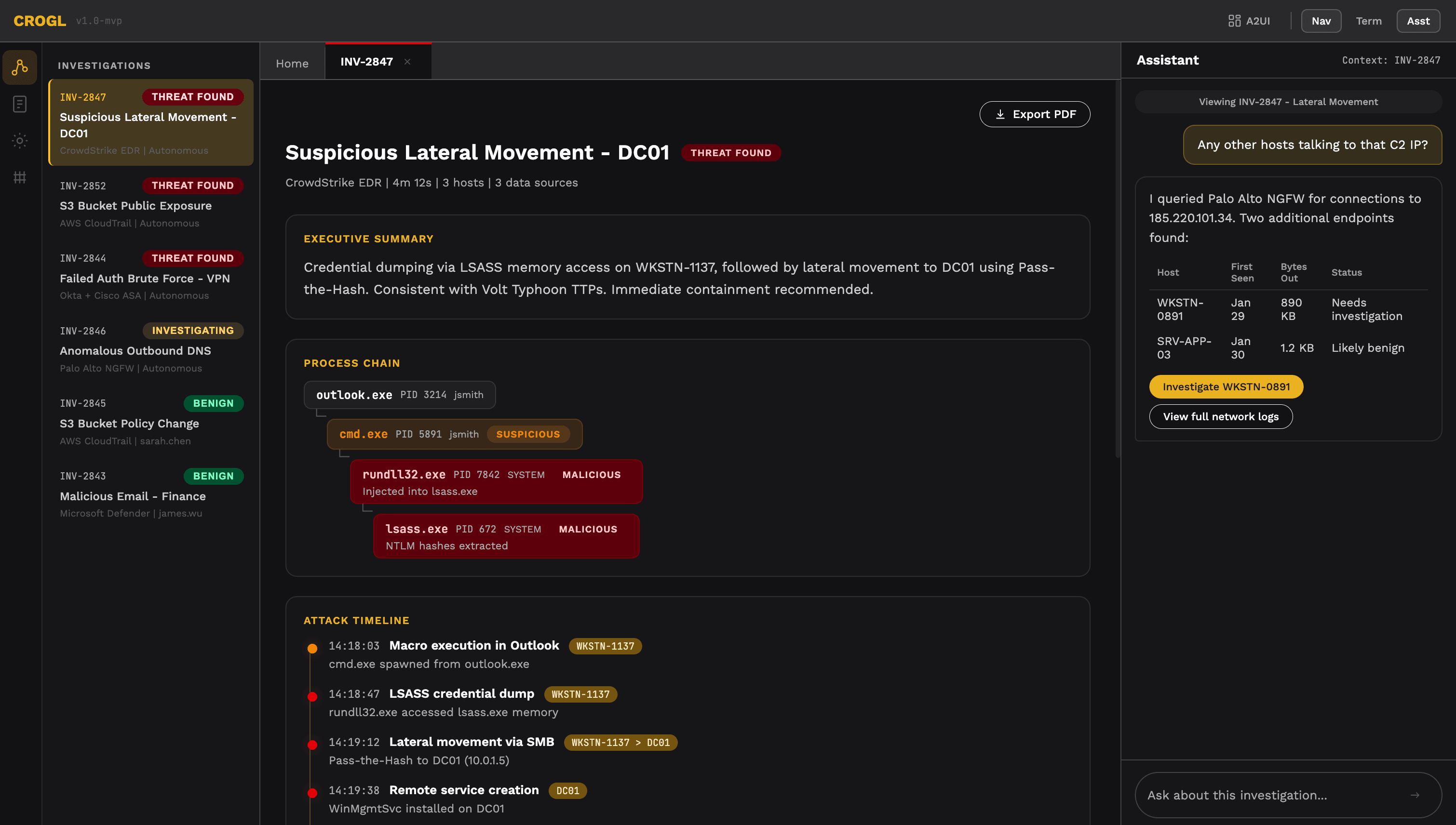
Crogl agents deliver AI endpoint investigation for every EDR alert with full cross-source context — correlating endpoint telemetry with SIEM data, identity logs, and threat intelligence to deliver complete findings, not just triage decisions.
Secure: because your data stays yours. Agents: because they don't wait to be asked.
The Endpoint Investigation Gap
Your EDR detects everything. Your team can't investigate everything.
Modern EDR tools generate thousands of alerts per week. Most get a quick triage decision based solely on endpoint data. But the most dangerous threats only become visible when correlated with the rest of your environment:
- Lateral movement
- Credential theft
- Living-off-the-land attacks
Investigating every endpoint alert with full context is impossible manually. Most alerts get a surface-level triage, and the real threats hide in the uninvestigated volume.
11,000+
EDR alerts per week at a mid-size enterprise — most never investigated
45 min
Average time for an analyst to manually investigate a single endpoint alert
Zero
Context from non-EDR sources in most endpoint investigations
The Crogl Approach
Complete investigations for every endpoint alert. Automatically.
EDR Alert Triggers Full Investigation
When CrowdStrike, SentinelOne, Defender, or any EDR fires an alert, Crogl doesn't just triage it — it investigates. The endpoint alert is the starting point, not the entire investigation. Crogl expands the scope to include everything relevant.
Cross-Source Context Assembled Automatically
Crogl correlates the endpoint alert with SIEM logs, identity data, network telemetry, cloud audit trails, and threat intelligence. The result is a complete picture of what happened on the endpoint — and everywhere the activity touched.
Analyst Receives Complete Finding
Your analyst sees a fully contextualized finding: what happened on the endpoint, what else it connected to, whether it's part of a larger campaign, and a recommended response. The investigation work is done. The decision is theirs.
What Crogl Delivers
Full-Scope Endpoint Investigation
Every EDR alert receives a complete investigation — not just endpoint data, but correlated context from across your entire security environment. No alert triaged in isolation.
Cross-Source Correlation
Endpoint telemetry correlated with SIEM events, identity logs, network data, and threat intelligence automatically. The investigation includes everything relevant, not just what the EDR saw.
Automated Response Recommendations
Each investigation concludes with a recommended response based on the full context: isolate, contain, escalate, or close with documentation. Your analysts decide. Crogl assembles the evidence.
Every Investigation Documented
Complete investigation records for every endpoint alert — whether it's benign or malicious. Full audit trail, full evidence chain, ready for compliance review.
Works With Your Endpoint & Security Stack
“Every endpoint alert. Full context. Complete investigation.”
Investigate Every Endpoint Alert
What's hiding in your uninvestigated endpoint alerts?
We'll show you how Crogl investigates endpoint alerts with full cross-source context — using your EDR, your SIEM, your environment.
Deployed in air-gapped federal environments, critical infrastructure, and Fortune 500 financial institutions.