Secure Agents for Security Operations
Not a Copilot.
An Autonomous Investigator.
Crogl deploys AI agents that conduct full security investigations autonomously using your tools, your workflows, and data that never leaves your environment. No prompt. No human trigger. No playbook required.
See It In Action
Real investigations. Real tools. Full autonomy.
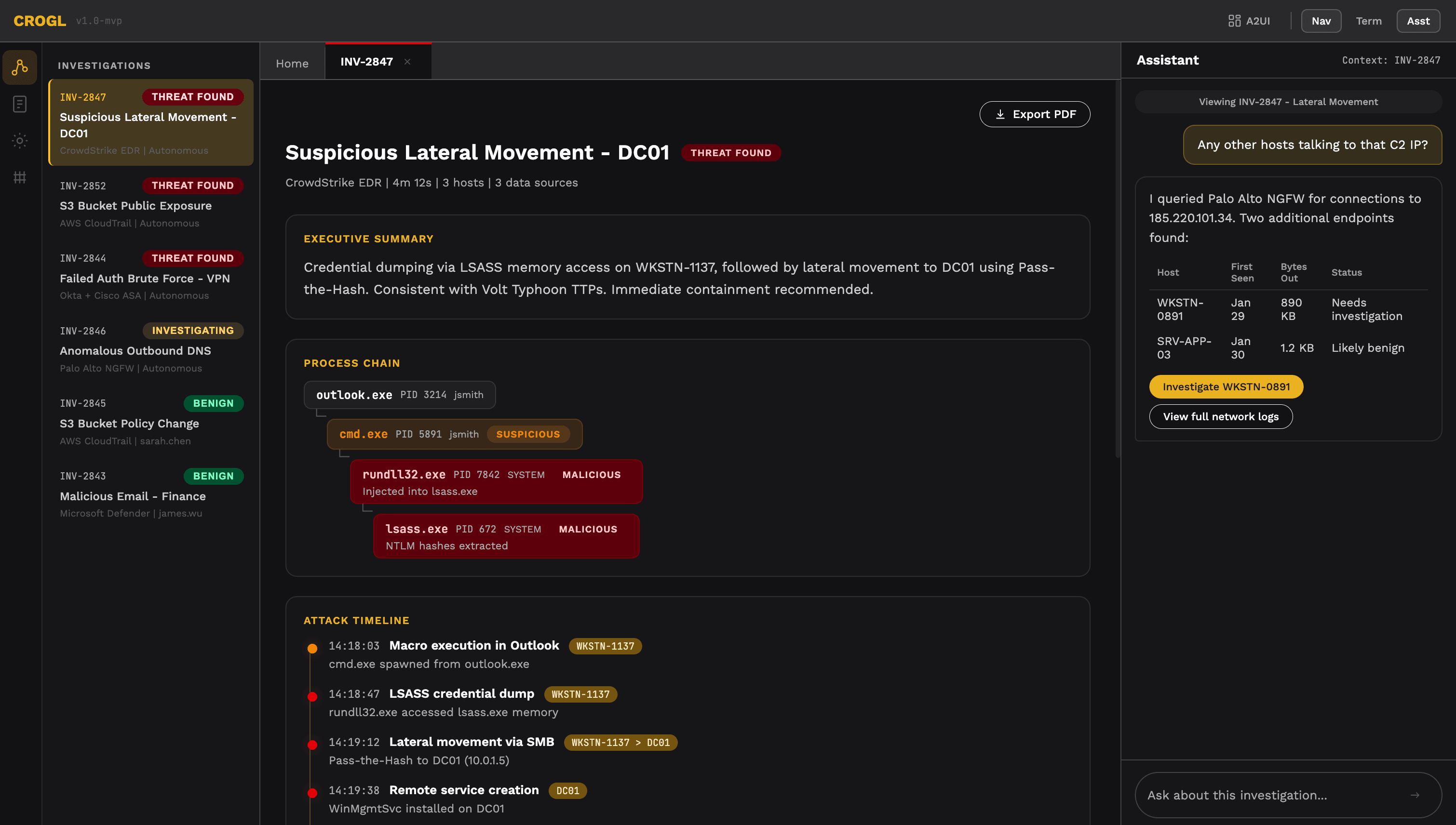
Every investigation is fully documented and auditable.
Crogl works across your existing tools. No schema mapping required.
How an Investigation Works
From alert to outcome.
Alert Arrives
An alert enters from your SIEM, SOAR, or ticketing system or any integrated source. Crogl detects it immediately. No polling delay. No queue. Threat intelligence advisories enter the same way. CRISP reports, ISAC advisories, and vendor bulletins all treated as first-class inputs.
Knowledge Graph Enriches
Before a single query runs, Crogl's knowledge graph contextualizes the alert. Who is the affected user? What assets are involved? What's their normal behavior? What related events have occurred? Context that would take an analyst 20 minutes to assemble manually is assembled in seconds.
Agents Execute the Investigation
Crogl agents run the investigation using your tools. Queries your SIEM, your EDR, your data lakes, and your threat intelligence feeds in their native format. No schema normalization. No hardcoded queries. The investigation follows your organization's workflows, adapted in real-time to what the data shows.
Documented. Closed or Escalated.
Every investigation, whether it closes as benign, escalates to an analyst, or triggers a response action is fully documented in your ticketing system. Complete audit trail. Every query. Every finding. Every decision. Analysts receive a finished investigation, not a raw alert.
The Technology That Makes Autonomy Possible
An LLM alone can't investigate a SOC alert. Context is the missing piece.
A user logs into your corporate network from New York at 2:00 PM. Four minutes later, the same user logs in from Prague. A standalone AI model sees two login events. An experienced analyst sees an impossible travel scenario and immediately asks deeper questions:
- Does this user VPN regularly? From Prague specifically?
- Are they accessing unusual assets in either session?
- What does the rest of their activity look like today?
Without those answers, automation is guesswork. With them, it's judgment.
Crogl's knowledge graph continuously maps your environment — users, assets, behaviors, relationships, access patterns, and history. Every alert is enriched against this live map before investigation begins. This is what enables Crogl to reason about novel threats, handle alerts it's never seen before, and produce investigations that reflect the full complexity of your environment, not just the data in a single alert.
Built Differently from the Ground Up
A system designed to investigate.
Most security AI is a single LLM integrated with an existing tool. The LLM generates a suggestion. The tool surfaces it. A human acts on it.
Crogl is different — a compound AI system with multiple components working together, each responsible for a distinct part of the investigation:
Knowledge Graph
Maintains live environmental context — entities, relationships, behaviors
AI Orchestration Layer
Plans and executes the investigation workflow autonomously
LLM(s)
Reasons over evidence, generates findings, writes documentation
Tool Integration Layer
Queries your existing security stack in native formats
No single component is responsible for the investigation. The system is. That's what makes it reliable on threats no one has written a rule for.
Your AI Policy. Your Models.
Crogl works with the models your organization trusts, including ones that never leave your environment.
Crogl is model-agnostic. Choose the LLM that fits your security requirements, compliance posture, and infrastructure constraints.
OpenAI
Via your organization's own API credentials
Anthropic Claude
Via AWS Bedrock — inference stays within your cloud
Self-Hosted OSS Models
Including large-scale private deployments — GPT-OSS-120B and equivalent
More integrations on the way.
This matters for federal and regulated environments where external model APIs are off-limits. Crogl can run fully self-hosted inference — the compound AI system operates entirely within your environment, with no data reaching any external endpoint.
Out-of-the-Box. Then Infinitely Extensible.
Production-ready on day one. Customizable from day two.
Crogl ships with a library of skills covering the core SOC workflow immediately:
Threat Hunting
Proactively searches your environment for indicators of compromise and adversarial behavior patterns
Alert Investigation
Conducts end-to-end investigation of any alert, routine or novel, across all integrated data sources
Report Creation
Generates fully documented investigation reports and impact analyses, ready for compliance and escalation
Beyond the built-in library, Crogl includes a skill builder where your team creates new skills using the same AI system that runs the platform. Define the workflow, the data sources, the outputs — Crogl executes it.
Every skill your team builds makes the system more capable in your specific environment. No vendor dependency. No waiting on a roadmap.
Works with Your Data As-Is
Stop normalizing. Start investigating.
Security data doesn't live in one place. It's distributed across SIEMs, data lakes, EDRs, cloud logs, and ticketing systems — each with its own schema, query language, and structure.
Traditional SOC automation requires all of it to be normalized before it can be used. That means months of schema mapping, integration work, and fragile pipelines that break every time a source changes.
Crogl queries each data source in its native format. No normalization pipeline. No schema expertise required. No reconfiguration when a source changes.
Before
- ×Schema mapping required
- ×Playbook authoring sprint
- ×Query language expertise per source
- ×Weeks of setup
- ×Breaks on novel alerts and schema changes
After
- ✓Connect your tools
- ✓Investigate immediately
Deploy in Your Environment. Your Terms.
On-premises. Private cloud. Air-gapped. Your choice.
On-Premises
Runs entirely within your data center. No outbound connections required.
Best for: Regulated industries, strict data residency requirements
Private Cloud
Deploy within your AWS, Azure, or GCP environment. Crogl never touches your data.
Best for: Hybrid enterprises, cloud-first organizations
Air-Gapped
Full functionality in completely disconnected environments. No external network access whatsoever.
Best for: Federal agencies, classified environments, critical infrastructure
All three deployment models deliver the same full capability. There is no reduced-feature on-prem edition. Crogl is built for constrained environments — not retrofitted for them.
Architecture
How Crogl Fits Into Your Stack
An end-to-end investigation platform that connects to your existing security tools.
CROGL SYSTEM ARCHITECTURE v2.2 — On-premises, private cloud, and air-gapped deployments
Try Crogl
The best way to evaluate Crogl is against your own stack.
Bring your SIEM, your data sources, your alert volume, your constraints. We'll show you exactly how Crogl investigates, using your environment as the demonstration.
Deployed on-premises, in private clouds, and in air-gapped federal environments.